TL;DR
- Open-source software is one of the most common sources of application security exposure.
- Traditional SCA tools report vulnerabilities — but rely on internal teams to fix them.
- Red Hawk SCA is a managed service that identifies and remediates open-source vulnerabilities.
- AI handles the majority of source-code fixes. Engineers validate and deploy.
- Automated SBOMs, continuous CVE scanning, and SLA-backed remediation create measurable risk reduction.
Security posture should be continuously maintained — not periodically reviewed.
The Open-Source Risk Gap in Modern Application Security
Modern applications rely on hundreds — sometimes thousands — of open-source components and third-party libraries.
What Are Open-Source Components?
Open-source components are reusable pieces of software developed through public projects and shared under open-source licenses.
Engineering teams incorporate these components into applications to accelerate development rather than building every capability from scratch. They can range from small utility libraries to full frameworks that power critical application functionality.
Most are distributed through public repositories and package managers such as GitHub, GitLab, or language-specific registries like PyPI or npm, and are maintained by communities of developers who continuously improve and update them.
While these components dramatically increase development speed, they also introduce dependencies that must be monitored and maintained over time.
What Is Software Composition Analysis (SCA)?
Software Composition Analysis (SCA) identifies and monitors open-source components within applications to detect security vulnerabilities, license risks, and dependency health.
SCA tools generate a Software Bill of Materials (SBOM), scan components against known vulnerabilities (CVEs), and help engineering teams understand and maintain their software supply chain.
That dependency increases the speed of development, but also expands the attack surface.
Open-source risk is now one of the most common sources of application security exposure .
The challenge is no longer vulnerability detection. It is operationalizing remediation at scale.
Traditional tools generate reports and push tickets to engineering teams. Remediation becomes manual, reactive, and delayed.
And delayed remediation increases:
- Operational risk
- Regulatory risk
- Reputational risk
Security posture slowly erodes. Not because teams don’t care, but because ownership is fragmented.
The exposure is not abstract. It is operational, and actively targeted.
Open-Source Software Security Risks
Open-source components are a frequent target for malicious actors. Exploited vulnerabilities can be leveraged for data theft, extortion, operational disruption, intellectual property compromise, or broader cyber intrusion.
When open-source vulnerabilities go undetected or unremediated, organizations face material risk, including:
- Data breaches
- System compromise
- Malware infiltration
- Service disruption or downtime
- Financial loss
- Reputational damage
- Loss of intellectual property
Open-source risk is not theoretical exposure. It is an active attack surface.
Codebases Contain 237 Unique Vulnerabilities on Average
The overall proportion of codebases containing at least one vulnerability remained mostly steady year-over-year, from 86% in 2024 to 87% in 2025, but the average number of vulnerabilities more than doubled, and the average number of unique vulnerabilities increased 54%. SC Media
Red Hawk SCA: A Managed Framework for Open-Source Risk Reduction
Red Hawk SCA is a managed service that continuously:
- Maintains deep technical documentation
- Identifies open-source vulnerabilities
- Actively remediates vulnerabilities in application source code
It shifts vulnerability management from manual, reactive engineering work to AI-driven remediation backed by defined service levels.
This is not passive monitoring.
It is managed execution.
Traditional SCA Tools Report Risk — They Don’t Reduce It
Open-source risk is persistent.
New vulnerabilities are disclosed daily. Applications accumulate technical debt over time. Engineering teams balance feature delivery against security remediation.
Without structured oversight:
- Vulnerabilities remain open
- Backlogs grow
- Security posture eroded
- Technical Debt grows
Proactive remediation reduces exposure and restores clarity.
Security should not depend on whether teams “get to it.”
It should be continuously maintained.
AI-Driven Vulnerability Remediation at Scale
Red Hawk SCA is built around outcomes.
- Vulnerabilities are remediated — not just reported
- AI accelerates remediation by identifying upgrade paths, updating vulnerable dependencies, and generating pull requests for engineering validation.
- Engineers validate changes instead of manually resolving issues
- Security posture is continuously maintained
This changes the operating model.
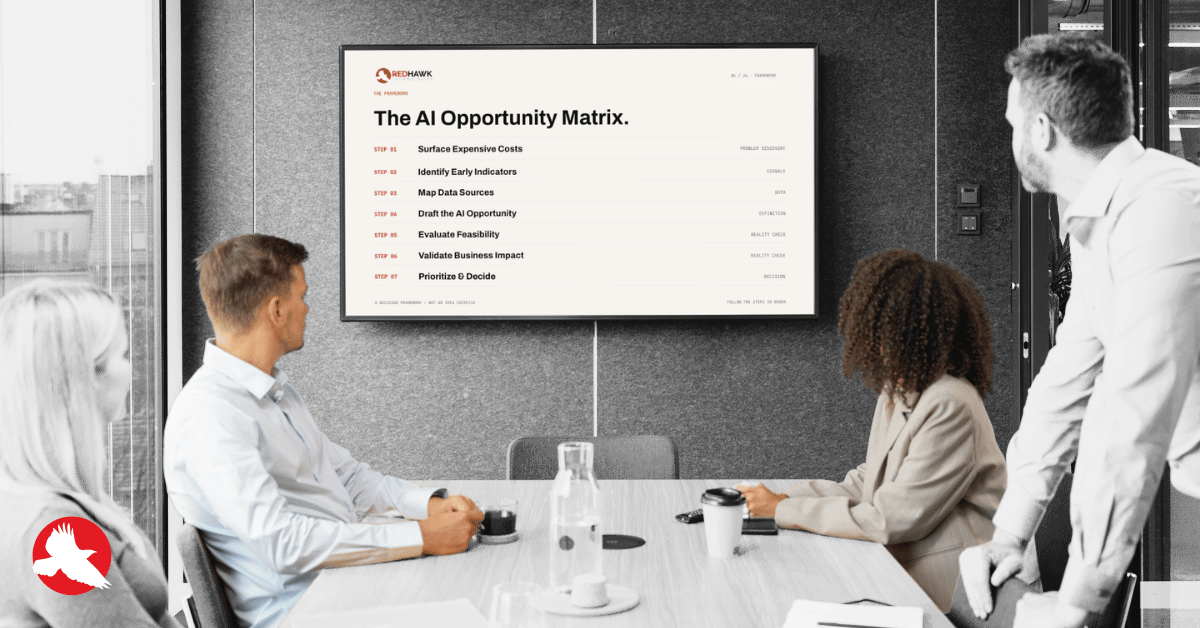
The Vulnerability Management Shift
| Traditional SCA Workflow | Continuous Remediation Model - Red Hawk SCA |
|---|---|
| Scan for vulnerabilities | Identify vulnerable dependencies |
| Generate reports | Generate AI-assisted remediation updates |
| Assign tickets to engineering | Validate fixes through engineering QA |
| Remediation delayed by backlog | Maintain continuous security posture |
Traditional SCA tools surface risk. Red Hawk SCA operationalizes remediation.
SBOM Generation and Continuous CVE Monitoring
Security maturity requires more than patching.
Red Hawk SCA provides governance-level visibility:
- Automated SBOMs with full component lineage: Software Composition Analysis acts like an ingredient label for your software, allowing teams to see exactly what their applications are built on.
- Continuous CVE scanning across repositories
- Open-source license analysis and compliance visibility
- Executive-level reporting and trend visibility
- SLA-backed remediation based on application complexity and business criticality
- Continuous technical documentation maintenance
This creates structured oversight.
Leadership gains clarity into:
- Risk exposure
- Remediation velocity
- Security trend direction
- Component transparency
Open-source risk becomes measurable.
Business-Level Security Outcomes
Red Hawk SCA is designed to produce tangible results :
- Reduced exposure to cybersecurity risk
- Faster mean time to remediation
- Lower reliance on manual engineering effort
- Faster understanding of inherited or undocumented systems through automatically generated architecture documentation.
- Increased confidence in application security posture
Security stops being reactive.
It becomes operationally managed.
Continuous Risk Reduction as an Operating Standard
Red Hawk SCA provides:
- Confidence that open-source vulnerabilities are being addressed proactively
- Automated Software Bill of Materials (SBOM) generation and maintenance.
- Continuous monitoring for publicly disclosed vulnerabilities (CVEs) affecting identified components.
- Severity-based vulnerability prioritization.
- AI-assisted remediation with pull-request-ready fixes.
- Human quality assurance and deployment support for remediated changes.
- Native integration with client development workflows and tooling, including Azure DevOps.
- Application-level and executive summary reporting for security trends and posture analysis.
- Real-time, AI-generated technical documentation for living system references, reducing dependency on tribal knowledge and improving maintainability.
Security posture should not drift. It should be actively maintained.
From SCA Monitoring to Continuous Risk Reduction
Open-source exposure is no longer a technical nuance — it is an enterprise risk variable.
Boards and executive teams are increasingly expected to understand:
- What software components exist inside critical applications
- How quickly newly disclosed vulnerabilities are addressed
- Whether remediation is structured or ad hoc
- How security posture trends over time
Reporting alone does not answer those questions.
Accountable remediation does.
Red Hawk SCA & Remediation establishes a defined operating model for open-source risk. It introduces continuous visibility, AI-driven execution, SLA-backed remediation, and governance-level reporting — transforming vulnerability management from reactive engineering work into a controlled security discipline.
The outcome is measurable:
- Reduced exposure
- Shorter mean time to remediation
- Lower manual dependency
- Greater executive confidence in application security posture
Security posture should not depend on available engineering capacity.
It should be continuously maintained, transparently measured, and operationally managed.
Red Hawk SCA delivers that standard.
Schedule a call to learn more and get a customized quote.
Software Composition Analysis (SCA) FAQs
What is Software Composition Analysis (SCA)?
Software Composition Analysis identifies and monitors open-source components within applications to detect vulnerabilities and license risks.
How is Red Hawk SCA different from traditional SCA tools?
Does Red Hawk generate SBOMs?
How are vulnerabilities remediated?
What outcomes can organizations expect?
Clarify and Define Your Big Idea
Use these easy-to-follow presentation slides to facilitate your own tech innovation workshop:
- Explore your vision for a new web or mobile app
- Define your goals and audience
- Outline logistics and required technology
- Move toward next steps in making your idea a reality

Download the Presentation
Reach New Heights
Read more articles about custom software development, mobile applications and technology trends from our team.
Flip the Script: Start with Your Business Problem, Not the AI Tool

Executive Guide to Building a Data Warehouse That Actually Supports AI